This is my experience when I want to copy the repository from the dvd to hardisk. I think the content of dvd is only copied to the hard drive and repository is ready for use. In fact there is a special way so that the repository can be legible by a daemon.
Needed:
Ubuntu 7.10 (gutsy gibbon)
Disk 1: main
Disk 2: main restricted multiverse
Disk 3: universe
Disk 4: universe
Disk 5: universe
Minimal empty harddisk is 25 gigabyte
OK, lets go...following this step!!
1. Create a folder to save the repository. usually stored in /home
:~$ sudo mkdir /home/ubuntu
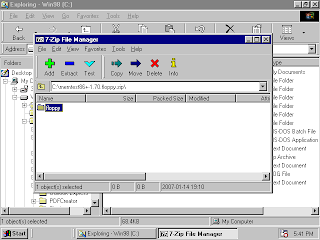
2. Then copyed the content of dvd 1 to folder /ubuntu with the following commant is (with the assumption that the program rsync is already installed) :
:~$ sudo rsync -avx –progress /media/cdrom0/. /home/ubuntu/.
if it has finished, repeat the above command again on the dvd 2 to dvd 5.
3. Each dvd has a list of package repositories that are stored in the dvd, so we must combine the list of packages that are in the DVD into a file package that can read the entire package is in the folder after copying from DVD. The first steps, create temporary folder to save the list of all packages from the dvd will be combined
:~$ sudo mkdir /tmp/main
Copy the file list for package MAIN Packages in DVD 1, entries DVD 1
:~$ sudo cp /media/cdrom0/dists/gutsy/main/binary-i386/Packages /tmp/main
4. Then combine the list of MAIN packages on the DVD 2 to list of Packages DVD 1 in the file /tmp/main/ with the following command:
:~$ sudo cat /media/cdrom0/dists/gutsy/main/binary-i386/Packages >> /tmp/main/Packages
5. After the merger is completed, move the files of package (/tmp/main/Packages) to the place where saved the main package that was copied from the earlier dvd with this command:
:~$ sudo cp /tmp/main/Packages /home/ubuntu/dists/main/binary-i386/
6. Then re-compress list of main packages :
:~$ cd /home/ubuntu/dists/main/binary-i386/
:~$ sudo gzip -9 -c Packages > Packages.gz
:~$ sudo bzip2 -9 -c Packages > Packages.bz2
7. Then combine file packages Universe from dvd 3 to dvd 5, the general command is the
same as the step 3 to step 6. create temporary folder to save the list of all packages from the dvd will be combined
:~$ sudo mkdir /tmp/universe
8. Change DVD2 with DVD 3 then copyed file of list universe packages
:~$ sudo cp /media/cdrom0/dists/gutsy/universe/binary-i386/Packages /tmp/universe
9. Combine list of universe package from DVD 4 with DVD 3 in folder /tmp/universe/Packages :
:~$ sudo cat /media/cdrom0/dists/gutsy/universe/binary-i386/Packages >> /tmp/universe/Packages
10. Combine list of universe package from DVD 5 with list of packages DVD 3 in folder /tmp/universe/Packages :
:~$ sudo cat /media/cdrom0/dists/gutsy/universe/binary-i386/Packages >> /tmp/universe/Packages
11. after combined, moving file packages (/tmp/universe/Packages) to the place where saved the main package that was copied from the earlier dvd with this command:
:~$ sudo cp /tmp/universe/Packages /home/ubuntu/dists/universe/binary-i386/
12. then re-compress list of Universe Packages :
:~$ cd /home/ubuntu/dists/universe/binary-i386/
:~$ sudo gzip -9 -c Packages > Packages.gz
:~$ sudo bzip2 -9 -c Packages > Packages.bz2
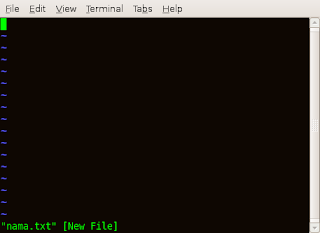
13. Then change file /etc/apt/sources.list with the command:
:~$ sudo gedit /etc/apt/source.list
and fill this statement in the first line :
deb file:///home/ubuntu gutsy main restricted universe multiverse
taraaaa.....the packages of repositori is ready to installed...
:~$ sudo rsync -avx –progress /media/cdrom0/. /home/ubuntu/.
if it has finished, repeat the above command again on the dvd 2 to dvd 5.
3. Each dvd has a list of package repositories that are stored in the dvd, so we must combine the list of packages that are in the DVD into a file package that can read the entire package is in the folder after copying from DVD. The first steps, create temporary folder to save the list of all packages from the dvd will be combined
:~$ sudo mkdir /tmp/main
Copy the file list for package MAIN Packages in DVD 1, entries DVD 1
:~$ sudo cp /media/cdrom0/dists/gutsy/main/binary-i386/Packages /tmp/main
4. Then combine the list of MAIN packages on the DVD 2 to list of Packages DVD 1 in the file /tmp/main/ with the following command:
:~$ sudo cat /media/cdrom0/dists/gutsy/main/binary-i386/Packages >> /tmp/main/Packages
5. After the merger is completed, move the files of package (/tmp/main/Packages) to the place where saved the main package that was copied from the earlier dvd with this command:
:~$ sudo cp /tmp/main/Packages /home/ubuntu/dists/main/binary-i386/
6. Then re-compress list of main packages :
:~$ cd /home/ubuntu/dists/main/binary-i386/
:~$ sudo gzip -9 -c Packages > Packages.gz
:~$ sudo bzip2 -9 -c Packages > Packages.bz2
7. Then combine file packages Universe from dvd 3 to dvd 5, the general command is the
same as the step 3 to step 6. create temporary folder to save the list of all packages from the dvd will be combined
:~$ sudo mkdir /tmp/universe
8. Change DVD2 with DVD 3 then copyed file of list universe packages
:~$ sudo cp /media/cdrom0/dists/gutsy/universe/binary-i386/Packages /tmp/universe
9. Combine list of universe package from DVD 4 with DVD 3 in folder /tmp/universe/Packages :
:~$ sudo cat /media/cdrom0/dists/gutsy/universe/binary-i386/Packages >> /tmp/universe/Packages
10. Combine list of universe package from DVD 5 with list of packages DVD 3 in folder /tmp/universe/Packages :
:~$ sudo cat /media/cdrom0/dists/gutsy/universe/binary-i386/Packages >> /tmp/universe/Packages
11. after combined, moving file packages (/tmp/universe/Packages) to the place where saved the main package that was copied from the earlier dvd with this command:
:~$ sudo cp /tmp/universe/Packages /home/ubuntu/dists/universe/binary-i386/
12. then re-compress list of Universe Packages :
:~$ cd /home/ubuntu/dists/universe/binary-i386/
:~$ sudo gzip -9 -c Packages > Packages.gz
:~$ sudo bzip2 -9 -c Packages > Packages.bz2
13. Then change file /etc/apt/sources.list with the command:
:~$ sudo gedit /etc/apt/source.list
and fill this statement in the first line :
deb file:///home/ubuntu gutsy main restricted universe multiverse
taraaaa.....the packages of repositori is ready to installed...
8:18 AM | 0
comments | Read More